
Overview of software features and capabilities
Core Impact Pro
Investigate multi-threat environments
Core Impact Pro is the only product that enables simulation of multi-step attacks and detects a chain of vulnerabilities that are critical to accessing your organization's assets and systems.
- Surveillance cameras vulnerability test
- Web services testing for web and mobile applications
- What-If attack analysis
This product detects and documents data at risk as well as the severity of security vulnerabilities by imitating an attacker method of exploiting vulnerabilities.
Perform real attacks and detect critical vulnerabilities:
Core Impact Pro software is the most comprehensive software to evaluate and test your organization's security vulnerabilities, which can include:
User systems
Passwords and identities
Mobile devices
Wireless networks
Web Services and Applications
Network systems and equipment
Core Impact Pro software with over 15 years of top-level security and research experience lets you evaluate the security of your organization by testing the latest methods used by cybercriminals today.
Sorena Secure Processing Company has a team of highly qualified experts who can supply, install and sell
Core Impact Pro software without delay.
Core Impact Pro software features
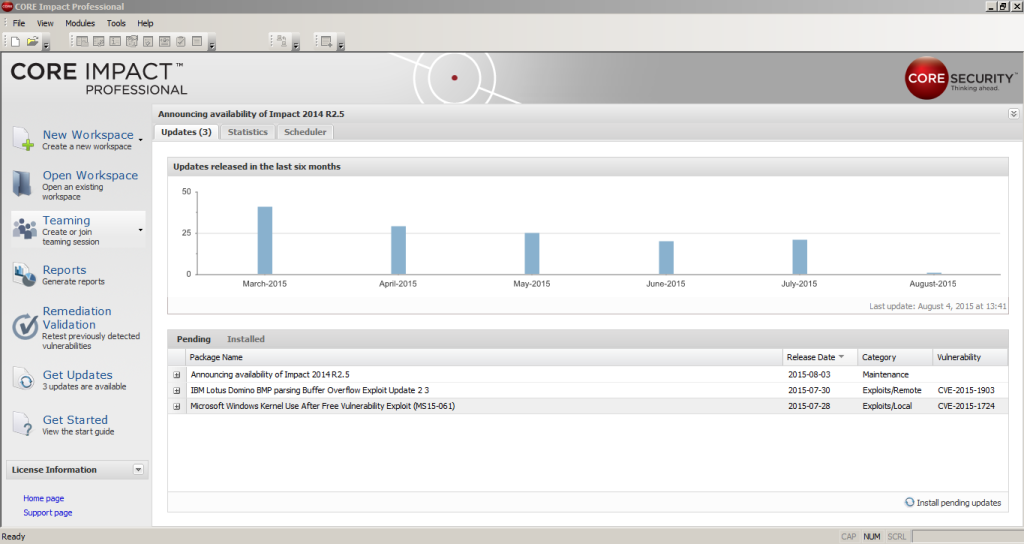
Business Exploits
Core Impact Pro software provides up-to-date real-time testing and evaluation capabilities. Core Impact Pro software offers more than 30 new exploits per month and a number of updates to other features. These exploits have all been professionally produced and tested by researchers and programmers at the company.
Team use
Experts are now able to interact and collaborate on a project with multiple copies of Core Impact Pro in a work environment. This feature provides a shared view of work.
reporting
Core Impact Pro software provides comprehensive reporting capabilities:
Reporting of exploitable vulnerabilities to plan for remediation
Reporting on criteria that illustrate the effect of the multilevel defense system.
Reporting in accordance with industry and government regulations
Vulnerability Reporting
ExCraft SCADA Plugin for Core Impact Pro
Core Security, in collaboration with ExCraft Labs, has developed improved SCADA exploits for use in Core Impact Pro software.
The ExCraft SCADA extension, which contains more than 50 exploits, can evaluate different types of SCADA systems from a security perspective. It also adds about 10 new exploits per month on average.

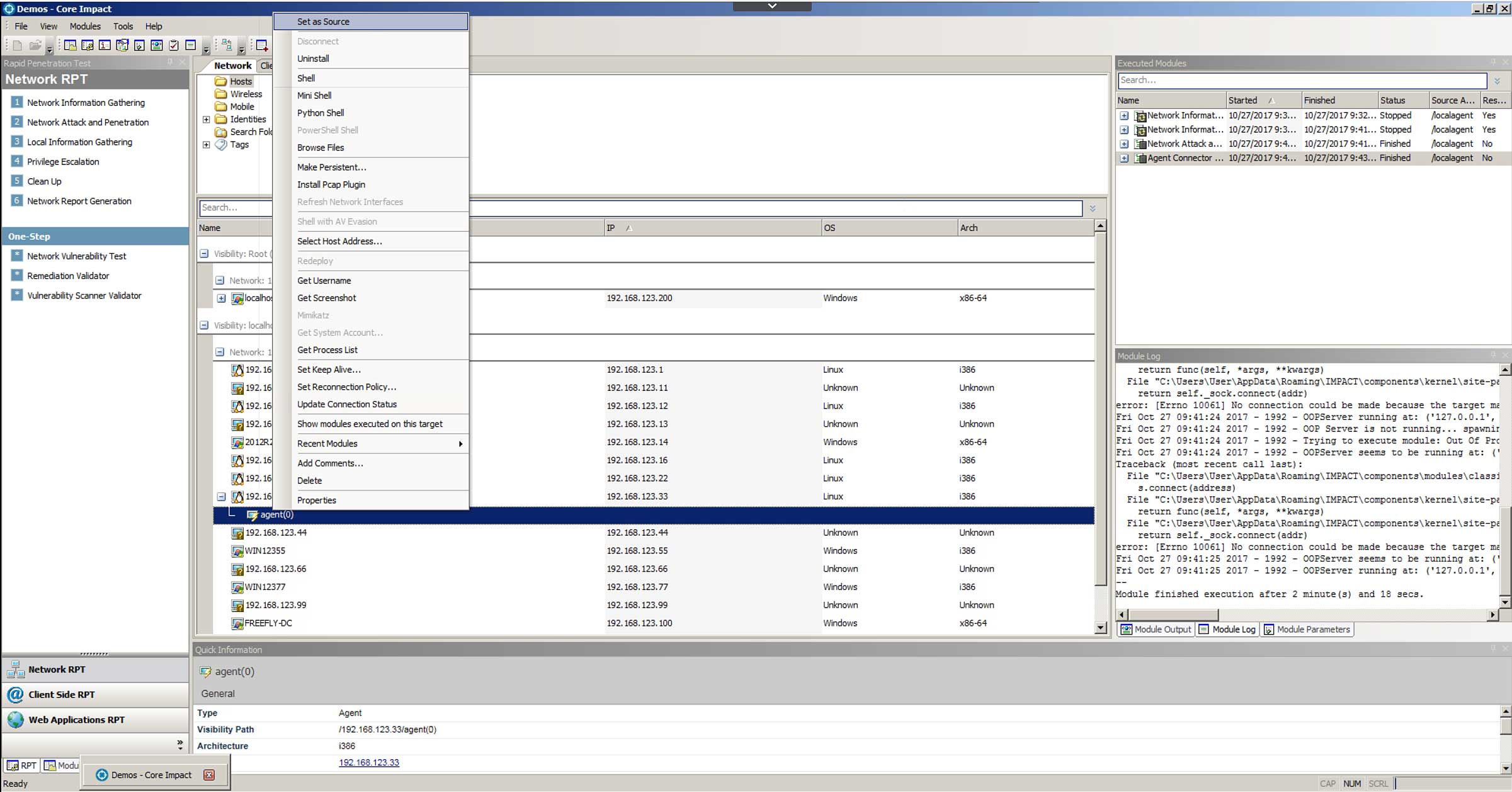
Network pentesting
- Gathering network information and creating system profiles
- Identify and exploit critical applications, services, devices, and operating system vulnerabilities
- Imitating attacker attacks to access and manipulate data
- Penetration into vulnerable systems as a base for attacking other network resources via VPN and Proxy
- Testing and evaluating defense technologies' ability to detect and stop attacks
- Testing client-side systems
- Crawl sites, search engines and the like for information on the intended purpose
- Create phishing emails manually or from existing examples
- Discover identities and passwords
- Discover the hashes associated with Windows NTLM and try to break them
- Discover identities such as usernames, passwords, SSH keys, and cookies
- The use of identified identities as part of multiple intrusion attacks in the intrusion testing process
- automatic control of the system through poor manual authentication or rapid penetration test (RPT)
Wireless network penetration test
Evaluation of WEP, WPA-PSK and WPA2-PSK encrypted networks
Perform man-in-the-middle attacks, intercept wireless traffic, and put exploits in traffic
Create fake Wifi access points and paste it instead of the intended Wifi system
CCTV attacks
Ability to discover CCTVs in the network and test their vulnerabilities
109/5000
Ability to prove camera vulnerabilities correctly with a sample video feed or access to the camera management interface
Test and evaluate camera video manually or via the automated RPT method
Web application penetration testing
Identify security vulnerabilities in web applications, web servers and related databases without false positives
Test all the web application vulnerabilities based on Owasp Top 10
Dynamic production of exploits to investigate security vulnerabilities in web applications
Ability to import and validate web vulnerability scanner results
Ability to attack web server and back-end network
Testing web services for web and mobile applications
Mobile device penetration test
Identify the critical vulnerabilities of mobile devices
Security assessment of new mobile devices and related web service
Access to all mobile numbers, GPS data and sms logs and calls
Providing Android Agent embedded for Android devices
Validation of the vulnerability scan
Core Impact Pro software can retrieve results from web and network vulnerability scanners and confirm that they can be exploited.
These scanners include:
| Acunetix® Web Security Scanner | eEye Retina® Network | Security Scanner | GFI LANguard™ |
| HP Web Inspect® | IBM AppScan® | IBM Internet Scanner® | Lumension® Scan |
| McAfee® Vulnerability Manager | TripWire IP360™ | Rapid7 AppSpider | Qualys QualysGuard® |
| SAINTscanner® | Tenable Nessus® | Tenable Security Scanner® | Cenzic Enterprise® |
Think like an attacker
The Core Security Assault Smart Platform helps you focus on resolving your most likely threats by modeling, simulating and testing what a real attacker can do.
Core Impact Pro software solutions
Core Security, with over 1400 customers worldwide, helps you discover and manage the most vulnerable parts of your IT business so you can have a secure business.
experiences
Our tested and successful products and solutions are backed by over 15 years of practical expertise in Core Security research laboratories and consulting services.

